The current situation report on IT security in Germany[1] was recently published by the BSI (Federal Office for Security and Information Technology) and, in addition to the risk situation, also contains solutions and offers for various target groups such as “Economy/Critical Infrastructures” or “Society/Citizens”. In this article we summarize the most important points regarding IT security for production and manufacturing companies.
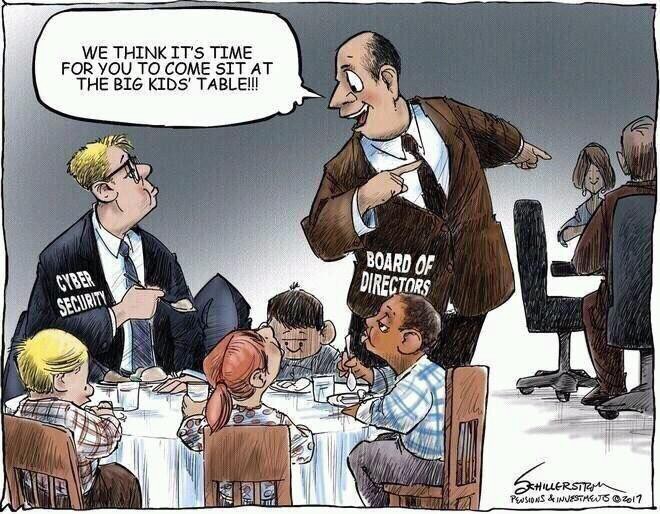
Picture: Roger Schillerstrom
An overall picture of the current threats and their criticality on the shop floor can only be obtained by taking a holistic view, since ultimately all persons involved are responsible for IT security both in development and in daily operations.
Basically, attacks are decreasing overall, but are becoming more targeted, more efficient and therefore more dangerous despite everything else. Thanks to freely available tools, APT (Advanced Persistent Threat) attacks, which were originally reserved for only a small group of participants with very high levels of expertise, are becoming constantly easier. The effort required for such attacks can thus be significantly reduced and the quality of the attacks increased. Cyber security is asymmetrical, to the great disadvantage of the operator of an IT infrastructure. While an attacker only must find one weak point, the operator must secure all attack vectors.
The most frequently used attack gateway in companies is and remains e-mail. Attachments are used decreasingly because they can be detected and blocked automatically by SPAM filters or other methods. Instead, there is a high momentum of its own when it comes to the further development of targeted social engineering attacks.
The best-known and most dangerous product classified by the BSI is currently the malware Emotet[2], which reads e-mails and contacts, evaluates them and distributes targeted information with malware to be reloaded. Once the problem is in the house, it can spread laterally to other networks such as the production network[3]. This occasionally is also referred to as spillover effects which lead to the fact that data and programs leave network segments in unwanted ways and emerge again in other ranges.
The malware introduced in this way mostly affects unpatched systems by exploiting their weak points, which are already publicly known. Especially in the shop floor, systems are patched only a few times a year, if at all. In the ideal case, the systems should be constantly busy, planned and especially all unplanned interruptions must be kept as low as possible. Finally, many manufacturers do not allow the change of the delivered system by introducing new software versions or even threaten with the loss of warranty.
BSI’s approach of obliging manufacturers to deliver safe products is a correct and important one, but what about the remaining warranty period? Does a manufacturer need to ensure the security of its system throughout the support period? This offers the potential for new support models but also raises new questions and challenges for mechanical and plant engineers. How, for example, can such a service be tested centrally and provided worldwide? How to deal with dependencies on external systems? If a manufacturer relies on Microsoft operating systems, it can no longer give a warranty for a period longer than two years under these conditions, since neither it nor Microsoft itself are presumably be aware now what the next LTSC release will involve. These challenges are likely to further benefit newly emerging projects such as ELISA (Enabling Linux In Safety Applications)[4], as companies from the affected environment themselves can intervene in research and control the development.
In critical infrastructures (KRITIS)[5], however, this can currently also mean that partially old technology in control systems must be replaced in accordance with the legal requirements by the BSI Kritis Ordinance (BSI-KritisV) in order to be able to guarantee protection according to the “state of the art”[6].
There is no panacea for IT security. Weak points for old threats are closed and new threats are created. No matter whether you segment your network, close interfaces or use multi-level malware scanners, clever heads will always find new ways to get the desired data or to manipulate or completely destroy it. In order to maintain a state as stable as possible, it helps companies only to regularly analyze the new threats, to (get to) know vulnerabilities, to reassess risks if necessary and to initiate countermeasures. Those who proactively implement uniform measures and, if necessary, can react promptly have the best chances. In the worst of all cases, this may involve restoring an up-to-date backup.
[2] https://www.bsi.bund.de/DE/Presse/Pressemitteilungen/Presse2019/Emotet-Warnung_230919.html
[3] https://www.bsi-fuer-buerger.de/BSIFB/DE/Service/Aktuell/Informationen/Artikel/emotet.html
[5] https://www.kritis.bund.de/SubSites/Kritis/EN/Home/home_node.html

Would you like to learn more? Do not hesitate to contact us, we will be happy to help you.


Here you can learn more about our company and our expertise as a pioneer and market leader.